Anomaly detection is the process of analyzing network traffic patterns that deviate from usual patterns and might represent network cyberattacks or threats. The aim of these attacks is to damage network functionality and deny the accessibility of services and hosts in the network. Among the various types of attacks, DDoS attacks stand out and can be divided into three main categories:
- Directed DDOS attacks
- Reflected DDOS attacks
- Amplification attacks
1.2.25.1 Directed DDoS attacks #
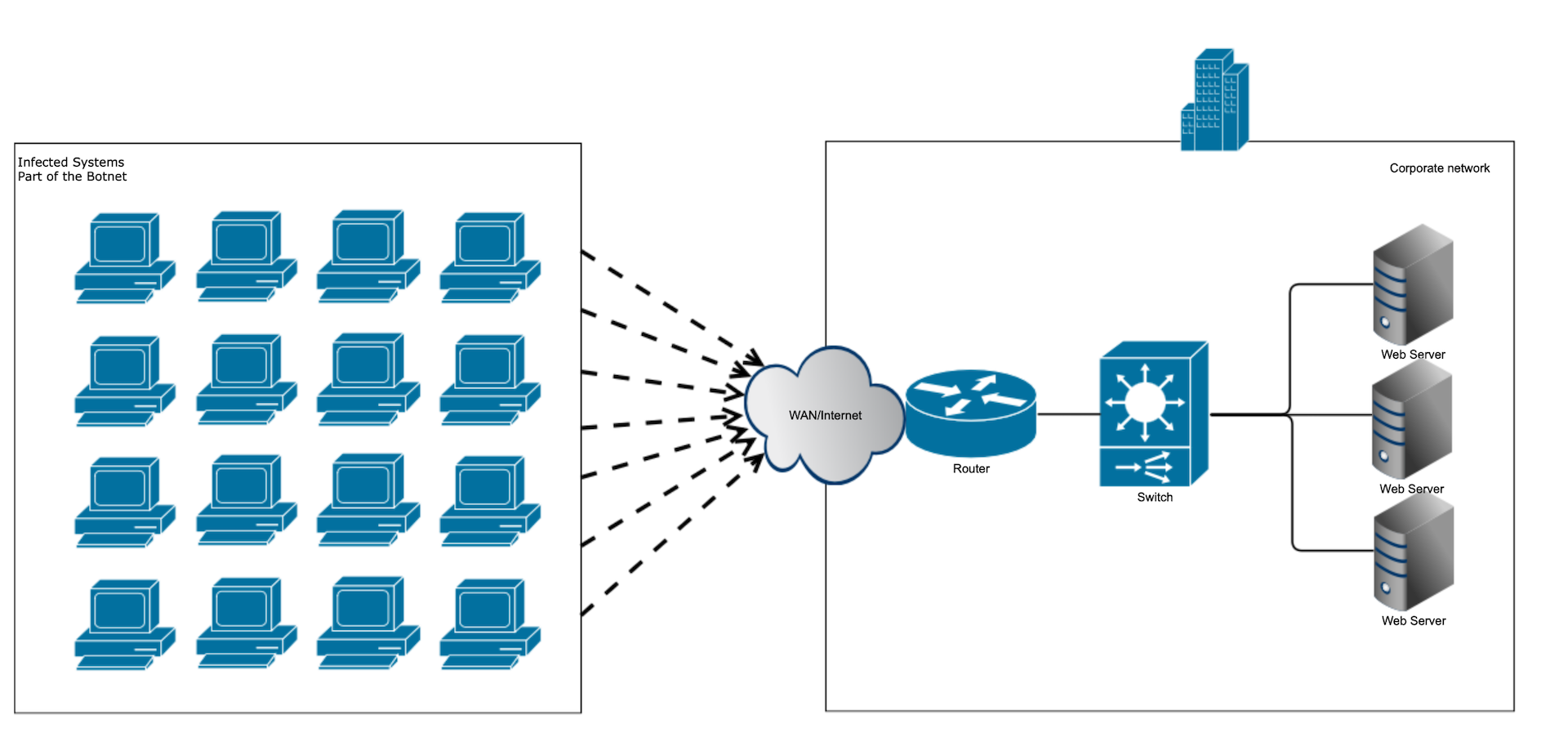
Directed DDoS attacks happen when the sources of attack generate the packets without considering a specific protocol or application and send them directly to the victim. Figure below depicts the typical
directed DDoS attack.
directed DDoS attack.
1.2.25.2 Reflected DDOS attacks #
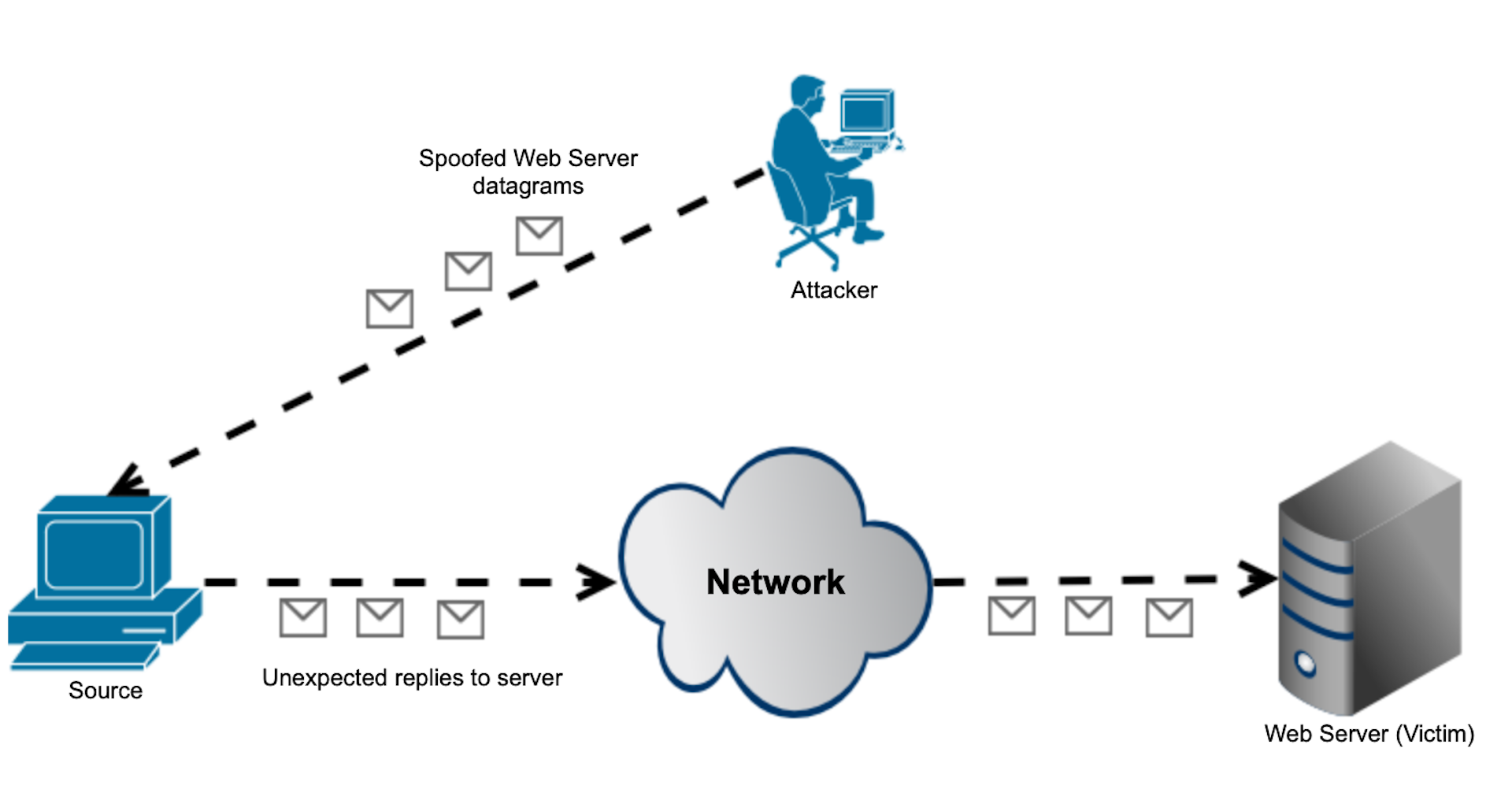
Reflected DDoS attacks happen when the sources of attack send spoofed packets that appear to be from a victim. Then, the source becomes the source of the DDoS by sending the response back to the victim.
The UDP protocol is easy to use for spoofing as it lacks the 3-way handshake mechanisms. Figure below depicts the typical reflected DDoS attack.
The UDP protocol is easy to use for spoofing as it lacks the 3-way handshake mechanisms. Figure below depicts the typical reflected DDoS attack.
1.2.25.3 Amplification attacks #
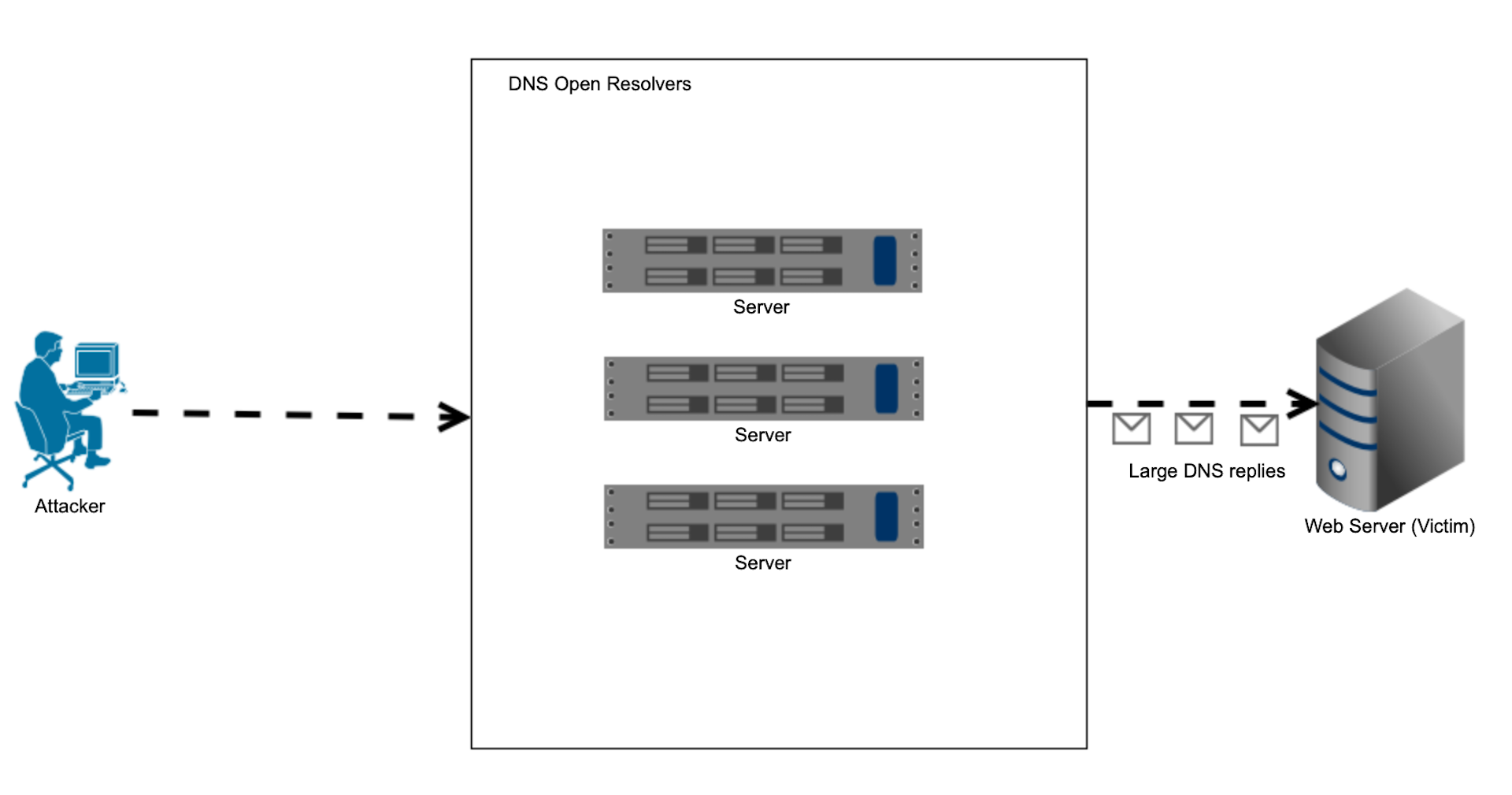
Amplification attacks are a kind of reflected DDoS attack when the spoofed packets represent queries to the internet open services that would respond to the victim with large volumetric replies (usually queries
are much smaller than replies). As a result, the victim receives a large number of replies, for which it never issues any queries. Figure below depicts the typical amplification DNS DDoS attack.
are much smaller than replies). As a result, the victim receives a large number of replies, for which it never issues any queries. Figure below depicts the typical amplification DNS DDoS attack.
1.2.25.4 SSH flood attacks #
SSH flood attacks target the customers’ infrastructure management, as SSH is the most commonly used protocol for remotely accessing the network nodes and hosts. The loss of access or the temporary management unavailability might cause significant issues during the network operations, as:
- Service disruption – legitimate users may be locked out
- Security breach – if a brute force attempt succeeds, the attacker gains access
- Resource exhaustion – server CPU/memory can be drained by handling excessive connections.
An SSH flood attack is a type of Denial of Service (DoS) or brute force attack that targets the SSH service:
- DoS-style flood: The attacker sends a large volume of TCP connection requests to port 22. The goal is to overwhelm the SSH daemon or the server’s network stack. This can slow down or crash the SSH service, preventing legitimate access
- Brute force flood: The attacker rapidly sends multiple SSH login attempts, trying to guess usernames/passwords. These are still TCP connections to port 22, but the focus is on authentication, not just flooding packets
1.2.25.5 DNS amplification attacks #
DNS amplification attacks are a type of Distributed Denial of Service (DDoS) attack that exploits the functionality of open DNS resolvers to flood a target system with an overwhelming amount of traffic. This attack leverages the disparity between small query sizes and significantly larger response sizes to amplify the volume of traffic directed at the victim, thereby disrupting services and rendering systems inaccessible. The attacker sends DNS queries with a forged source IP address, which is set to the IP address of the intended victim. These spoofed queries are sent to open DNS resolvers – servers that respond to queries from any IP address. The DNS resolvers process the queries and send responses back to the spoofed IP address (the victim). Since DNS responses can be much larger than the queries, this results in an amplification of traffic. The victim’s system becomes overwhelmed by the large volume of unsolicited DNS responses, leading to degraded performance or complete unavailability of services.
1.2.25.6 NTP amplification attacks #
NTP amplification attacks are a type of Distributed Denial of Service (DDoS) attack that exploits the Network Time Protocol (NTP) to overwhelm a target system with a flood of traffic. By sending small, spoofed requests to vulnerable NTP servers, attackers can generate significantly larger responses directed at the victim, effectively amplifying the attack’s impact. The attacker sends NTP requests with the source IP address forged to appear as the victim’s IP. These requests are sent to publicly accessible NTP servers that support specific commands, like monlist, which returns large requests about the last 600 hosts that requested anything from this specific NTP server. The victim’s network becomes overwhelmed by the high volume of unsolicited NTP responses, leading to service degradation or outage.
1.2.25.7 UDP flood attack #
UDP flood attacks are a type of Denial-of-Service (DoS) or Distributed Denial-of-Service (DDoS) attack that exploits the User Datagram Protocol (UDP) to overwhelm a target system with a high volume of traffic, leading to service disruption. The victim is checking for the application that might listen to the UDP packets, and in case when no application is found, it will respond with an ICMP destination unreachable. The process consumes victims’ resources and can lead to host outage or service disruption.
1.2.25.8 Smurf attacks #
Smurf attacks are a type of Distributed Denial-of-Service (DDoS) attack that exploits the Internet Control Message Protocol (ICMP) and IP broadcast addressing to overwhelm a target system with a flood of traffic. Typically, the attacker sends ICMP echo request packets with the spoofed source IP address to appear as the victim’s IP address. These spoofed packets are sent to an IP broadcast address of a network. A broadcast address directs the packet to all devices on that network segment. Upon receiving the ICMP echo request, each device on the network responds with an echo reply to the spoofed source IP(the victim). This results in a multiplication of traffic directed at the victim. The victim’s system becomes inundated with ICMP echo replies, consuming bandwidth and processing resources, leading to degraded performance or complete unavailability of services.
1.2.25.9 SYN flood attacks #
SYN flood attacks is a type of Denial-of-Service (DoS) or Distributed Denial-of-Service (DDoS) attack that exploits the TCP three-way handshake process to overwhelm a target system, rendering it unresponsive to legitimate traffic. In a typical TCP connection, the following three-way handshake occurs:
- SYN: The client initiates a connection by sending a SYN (synchronize) packet to the server.
- SYN-ACK: The server acknowledges the request by sending a SYN-ACK (synchronize-acknowledge) packet back to the client.
- ACK: The client responds with an ACK (acknowledge) packet, establishing the connection.
In a SYN flood attack, the attacker sends many SYN packets to the server but deliberately does not complete the handshake by sending the
nal ACK. This results in numerous half-open connections, consuming the server’s resources and potentially leading to service disruption.
1.2.25.10 ACK flood attacks #
ACK flood attacks is a type of Distributed Denial-of-Service (DDoS) attack that targets the Transmission Control Protocol (TCP) by inundating a server or network device with a massive volume of ACK(Acknowledgment) packets. These packets are typically used to confirm the receipt of data in a TCP connection. However, in an ACK flood attack, the attacker sends a large number of these packets without
any associated data or established connection, overwhelming the target’s resources and leading to service disruption. In a standard TCP communication, the ACK packet is part of the three-way handshake
process and subsequent data transfer, confirming the successful receipt of data. In an ACK flood attack:
any associated data or established connection, overwhelming the target’s resources and leading to service disruption. In a standard TCP communication, the ACK packet is part of the three-way handshake
process and subsequent data transfer, confirming the successful receipt of data. In an ACK flood attack:
- Flooding with ACK Packets: The attacker sends a deluge of TCP ACK packets to the target system.
- Resource Consumption: Each ACK packet prompts the target’s system to check for a corresponding active session. Since these ACK packets are unsolicited and not part of any established connection,
the system expends resources processing them. - Service Disruption: The excessive processing required for these illegitimate ACK packets can exhaust the target’s resources, leading to degraded performance or complete service unavailability.
This type of attack is particularly effective against stateful devices like firewalls and intrusion detection systems, which maintain records of active connections and are compelled to process each incoming ACK
packet, even if it’s illegitimate.
packet, even if it’s illegitimate.
1.2.25.11 HTTP(s) flood attacks #
HTTP(s) flood attacks are a form of Distributed Denial-of-Service (DDoS) attacks that targets the application layer (Layer 7 of the OSI model). It aims to overwhelm a web server or application by sending a massive volume of seemingly legitimate HTTP or HTTPS requests, thereby exhausting server resources and rendering the service unavailable to legitimate users. Unlike lower-layer attacks that exploit protocol vulnerabilities, HTTP(s) flood attacks mimic legitimate user behavior, making them harder to detect and mitigate. Attackers often utilize botnets – networks of compromised devices – to generate a high volume of requests.