For years, enterprise cloud networking was built around a simple assumption: pick a primary cloud provider, connect the data center to it, and expand from there. That model no longer reflects how many organizations actually operate. Today,...
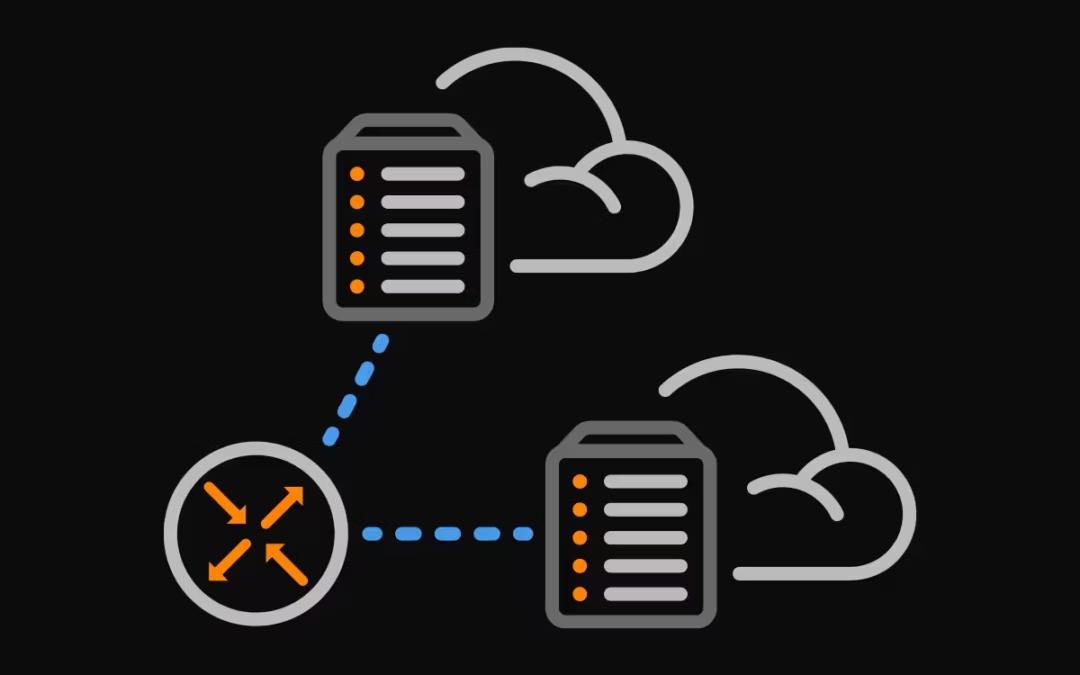
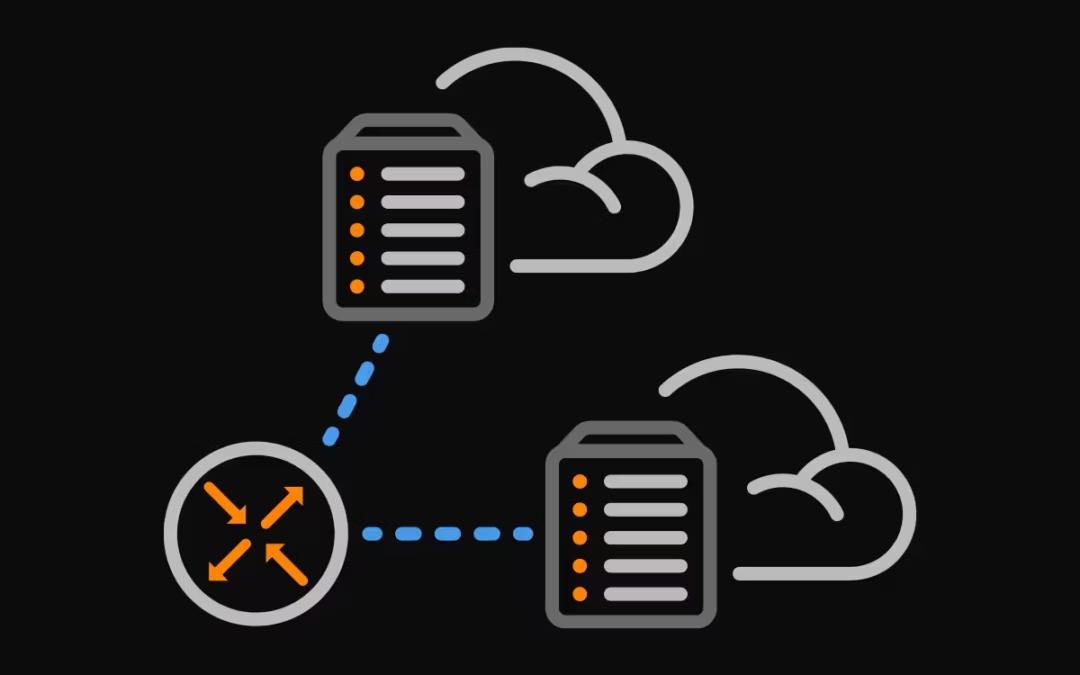
For years, enterprise cloud networking was built around a simple assumption: pick a primary cloud provider, connect the data center to it, and expand from there. That model no longer reflects how many organizations actually operate. Today,...
The Internet routing security story of the past decade has largely been about fixing route origins. RPKI Route Origin Validation (ROV) gave operators a...
For over three decades, BGP’s AS_SET path segment has been a legal, if problematic, feature of Internet routing. In May 2025, the IETF formally ended that...
If you've spent time supporting AI infrastructure, whether that's a GPU training cluster, a fleet of inference nodes, or a multi-tenant model serving...
Commit Control is a core safety mechanism in the Noction Intelligent Routing Platform (IRP). It governs how routing changes are applied by enforcing...
Modern IP networks operate at a scale where abnormal traffic patterns can emerge faster than operators can react. Sudden traffic spikes, protocol floods, or...
Border Gateway Protocol (BGP) is not merely a protocol—it’s the backbone of the internet. For service provider engineers and network architects, BGP is an...
In recent years, the concepts of Artificial Intelligence (AI) and Machine Learning (ML) have moved from the academic realm to the forefront of many...
Recent disruptions to two undersea internet cables in the Baltic Sea have yet again highlighted a pressing issue for businesses worldwide: the vulnerabilities...
Understanding BGP states is essential to grasp how BGP operates. Similar to interior gateway protocols (IGPs) like EIGRP, OSPF, or ISIS, BGP establishes...
In networking, communication between devices relies on the efficient exchange of data packets. Among the essential elements in this exchange are the ACK...
What is asymmetric routing? Asymmetric routing is a network communication scenario where the forward and reverse paths of network traffic take different...
The Mail Analogy: Understanding TCP Headers and Reliable Delivery The internet seamlessly transfers data, but how does it ensure everything arrives correctly?...