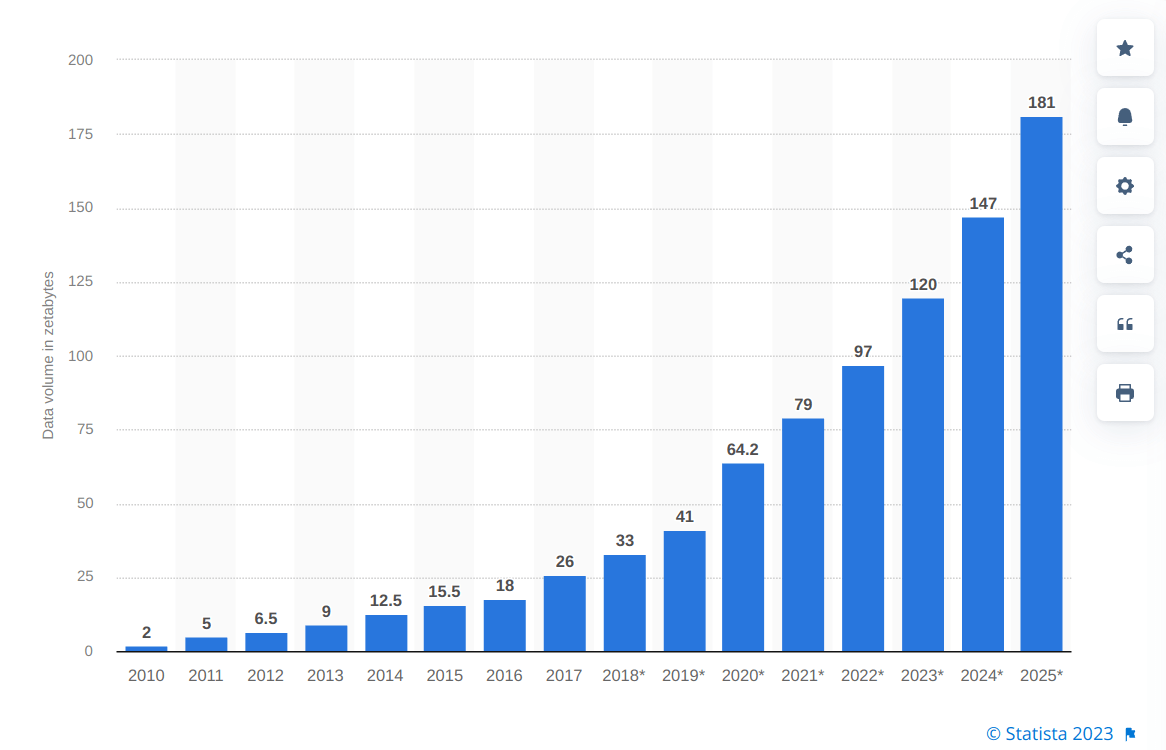
Figure 1 – Volume of data/information created, captured, copied, and consumed worldwide from 2010 to 2020, with forecasts from 2021 to 2025
source: https://www.statista.com/statistics/871513/worldwide-data-created/
Edge computing use case examples
Autonomous vehicles
Autonomous vehicles rely heavily on real-time data processing and decision-making, which can be challenging to achieve using traditional cloud computing architecture. With edge computing, the processing and decision-making can be done locally on the vehicle or at the network edge, reducing latency and ensuring that decisions can be made quickly and accurately.
For example, an autonomous vehicle can use sensors to detect objects in its surroundings and then use edge computing to analyze that data and make real-time decisions about how to navigate. This can include identifying obstacles, calculating safe distances, and determining the optimal route to take. By processing this data at the edge, the vehicle can make decisions quickly and accurately without relying on a centralized cloud server.
Surveillance
Edge computing can provide several benefits when it comes to surveillance cameras. By moving the computation of video analytics to the network edge, each camera can analyze its own footage and send only relevant data to the cloud server, reducing the amount of video data that needs to be transmitted and processed. This results in reduced bandwidth usage and lower latency, enabling faster response times for critical security events.
Furthermore, edge computing enables real-time video data processing, allowing for immediate detection and notification of security breaches or other critical events. This can improve overall security by enabling quick responses to potential threats.
Network Optimization
Edge computing products can be used to optimize network performance by measuring the performance of users across the internet and using analytics to determine the most reliable and low-latency network path for each user’s traffic. This is often referred to as network edge optimization or traffic steering.
Using edge computing to steer traffic across the network for optimal time-sensitive traffic performance, organizations can improve the user experience and ensure that critical applications and services are delivered with minimal latency and maximum reliability. This is particularly important for applications that require real-time or near-real-time data processing, such as video conferencing, gaming, and virtual reality.
Noction Intelligent Routing Platform
Noction IRP is an edge computing solution that operates at the network edge and analyses traffic in order to detect network congestion and blackouts. It uses BGP to manage traffic across multiple internet service providers (ISPs) and direct traffic over the best available path based on real-time network conditions.
Some key features of the Noction Intelligent Routing Platform include:
- Network performance monitoring: IRP continuously monitors network performance and analyzes network congestion, latency, and packet loss to determine the best path for traffic routing.
- Traffic steering: The platform automatically directs traffic across multiple ISPs and Internet Exchanges, optimizing traffic routing based on real-time network conditions.
- Traffic filtering: IRP filters traffic based on various criteria, such as traffic type, source, and destination, to optimize traffic routing and reduce network congestion.
- Dynamic path selection: The platform dynamically selects the best available path for traffic routing based on real-time network conditions, ensuring that traffic is always routed over the most optimal path.
- Network analytics: IRP provides detailed analytics and reporting on network performance, enabling organizations to identify and resolve network issues more quickly and efficiently.
IRP is an important instrument for optimizing network performance and ensuring that users receive the best possible experience when using time-sensitive applications and services. By using edge computing to steer traffic across the network, organizations can improve their systems’ efficiency and reliability while reducing costs and improving overall performance.
Conclusion
Edge computing can help prevent bandwidth exhaustion by reducing the amount of data that needs to be transferred over a network. In traditional cloud computing models, data is processed and stored in centralized data centers, which can result in large amounts of data needing to be transferred between the data center and the end user. This can lead to network congestion and bandwidth exhaustion, especially when many end-user devices are accessing the same data center.
With edge computing, however, data processing and storage occur closer to the end-user device, often at the edge of the network. This can reduce the amount of data that needs to be transferred over the network, as only the relevant data or processed results are sent back and forth between the end-user device and the edge computing device. However, it’s important to note that edge computing is not a silver bullet solution to bandwidth exhaustion. Other factors, such as network capacity and the number of IoT devices, play a role.
The cost of deploying and managing an edge computing environment can be significant and may exceed the project’s financial benefits. The upfront costs of building and maintaining an edge computing infrastructure, including the hardware, software, and networking components, can be high. Additionally, ongoing maintenance and upgrades can further add to the overall cost.
To address these challenges, it’s essential to carefully consider the costs and benefits of an edge computing project before embarking on it. This may involve conducting a thorough cost-benefit analysis and developing a comprehensive plan for managing the infrastructure over time. Additionally, it’s important to consider how the project can be scaled as the number of IoT endpoints grows and to plan for future expansion from the outset.




