One of the most significant additions in this release is the introduction of BGP Redirect and FlowSpec Redirect threat mitigation mechanisms.
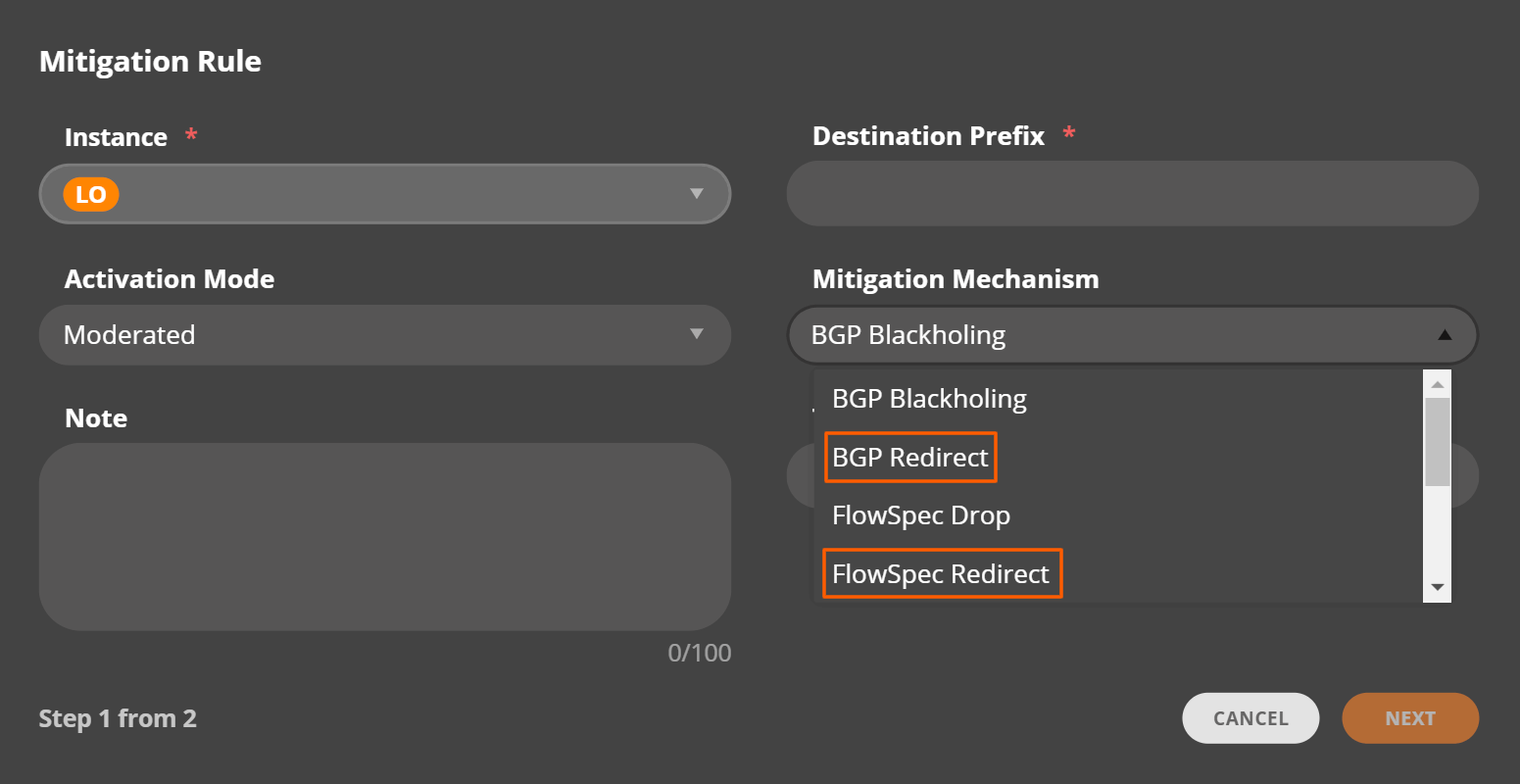
- The BGP Redirect mechanism allows network professionals to preset specific automatic or manual threat mitigation rules that, when triggered, tag a particular route with a BGP community value and subsequently signal client or provider routers to apply specific actions or policies to such routes.
- The FlowSpec Redirect mechanism lets IRP users automatically redirect specific traffic to an IP address for further processing or inspection, e.g., a scrubbing center. The DDoS scrubbing service can then analyze traffic and block or rate-limit malicious traffic while allowing legitimate traffic to pass through.
It’s worth noting that both FlowSpec Redirect and BGP Redirect mechanisms can be enabled for a single rule, with the thresholds for Flowspec being indicated lower than the Blackholing values. In this case, the BGP Mitigation comes into play when the FlowSpec Mitigation cannot handle the attack.
In addition, we’ve also introduced the ability to indicate the subnet size for threat mitigation rules. This gives IRP users even more control over their networks and allows them to take action in a more targeted and effective way.
Other improvements
Some other improvements and features in IRP v 4.1.1 include support for MFA in LDAP authentication, the introduction of Failover and Commit Control setup wizards, enhancement of the Global Search tool, the addition of a new (timeout) parameter to SNMP hosts, and more.
For more information on the complete set of features and improvements available with IRP 4.1.1, please contact Noction account representatives at sales@noction.com or review the documentation.
Alternatively, request a personalized demonstration of the product, and we’ll be in touch.