 Whether you are an experienced network administrator or you have just started to learn Border Gateway Protocol (BGP), Looking Glass (LG) is definitely a topic you should not ignore.
Whether you are an experienced network administrator or you have just started to learn Border Gateway Protocol (BGP), Looking Glass (LG) is definitely a topic you should not ignore.What is BGP Looking Glass?
Looking Glass (LG) servers are a real-time source of routing and BGP related information for network administrators. Looking Glass servers are deployed in different parts of the Internet and allow on-line checking of prefixes, collected from the BGP speaking routers. LGs make network administrators more effective during troubleshooting, helping them “see” their prefixes from the “outside”. In the second case, LG helps Internet users to understand how the BGP speaking routers interconnect Autonomous Systems (AS). Thanks to LG servers, Border Gateway Protocol newbies can touch a real networking “world” instead of running simple BGP topologies on buggy network simulators.
So, the question is what is LG and what is a motivation behind building BGP Looking Glass servers. LG software is basically a CGI script which creates an html page stored on a publicly accessible web server. An LG server acts as a user friendly front-end for BGP speaking routers. It sends read-only (usually show) commands to selected BGP routers within a certain AS and displays the output on a web page. For instance, a user selects bgp summary option on the web page lg.eastlink.ca for AS 7018 using a web browser (e.g. Mozilla Firefox). The result of the command – a list of the BGP peers along with their AS numbers, up/down time states, the number of received prefixes and other counters and statistics is displayed from AS 7018 perspective.
Showing BGP related information from remote BGP speaking routers is the main purpose for which LG servers are built. A good example of using LG server can be the checking of the upstream provider BGP table after a change in announced prefixes. For instance, after adding new prefixes with a network command a network administrator wants to be sure the new routes are visible on the upstream provider BGP routers. However, the administrator has no remote access to the routers. The desired solution is to connect to the provider’s LG server via web browser and to check BGP there. If the new prefixes are inserted into the BGP table of the provider’s’ routers, the administrator can continue with the next step. It would be finding out whether the prefixes are not blocked somewhere else on the Internet. The administrator will connect to a different LG server built for another AS and inspects BGP table there.
Web Based Looking Glass Servers
A general list of web based LG servers is available here. Let’s have a look at one of them – Eastlink LG server on lg.eastlink.ca. We are going to check an active route from AT&T (AS7018) to Google network 8.8.8.0/24. To do it, select AT&T (AS7018) under the Node column and type network 8.8.8.0/24 under the column Additional Parameters. Then press the Submit button. It is shown on the Picture 1.
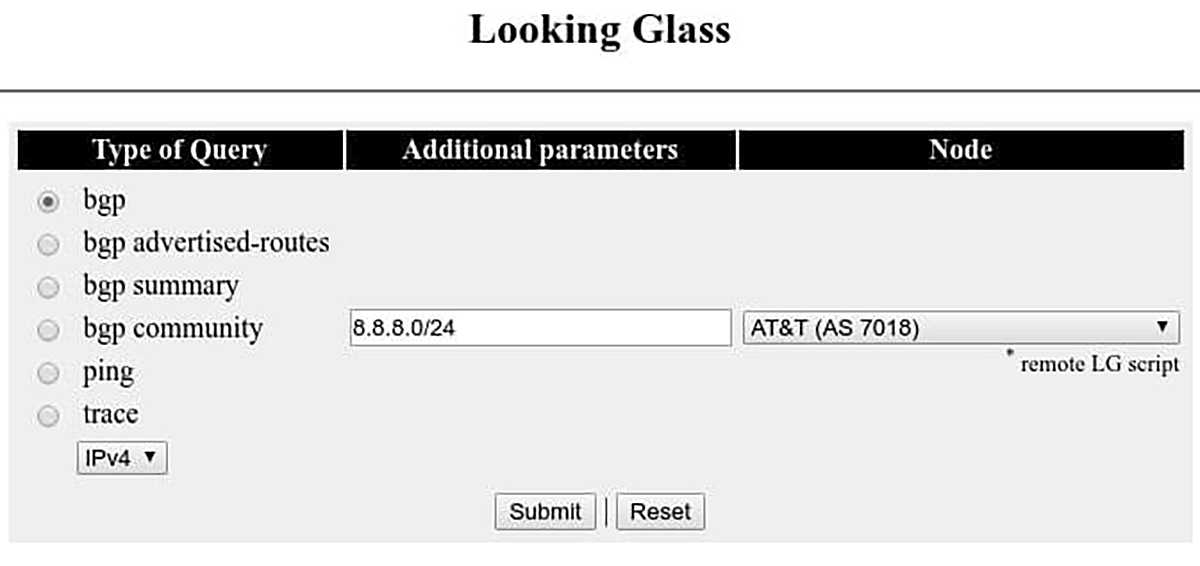
Picture 1 – Eastlink Looking Glass Server Web Interface
The truncated output of the BGP 8.8.8.0/24 command is shown on the Picture 2. As we can see, a route to the prefix 8.8.8.0/24 refers to path via AS7018 and AS15169 with the next hop IP address 12.0.1.1.
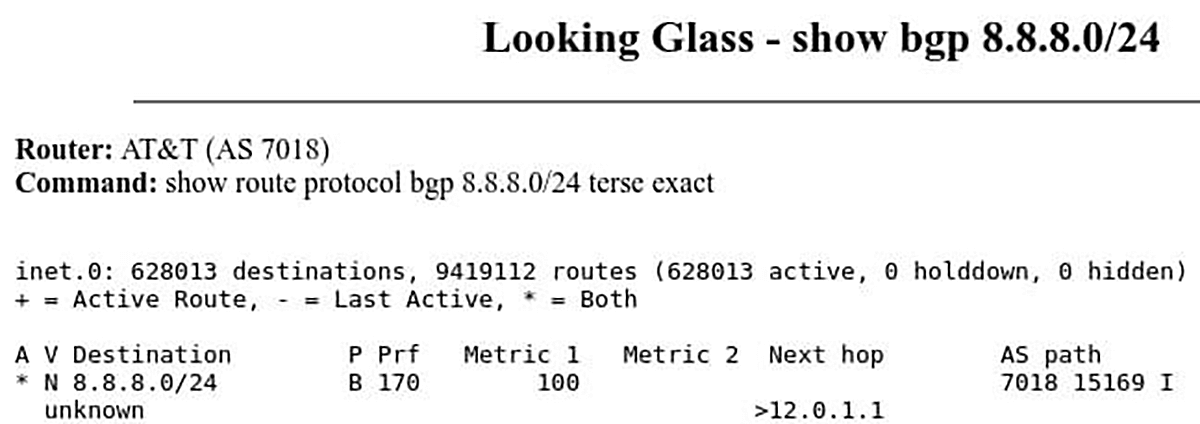
Picture 2 – Active Route to Google Prefix 8.8.8.0/24 from AT&T AS7018 – Eastlink Looking Glass Server
We already know that AS 7018 is assigned to AT&T company. To get more information on AS15169 we will use Hurricane Electric BGP Toolkit page. The page gives us a bunch of useful BGP IPv4 and Ipv6 information and statistics about the AS15169 which is assigned to Google Inc. For instance, we can display assigned IPv4 prefixes used by Google or to show its IPv4 BGP peers with AS 15169.
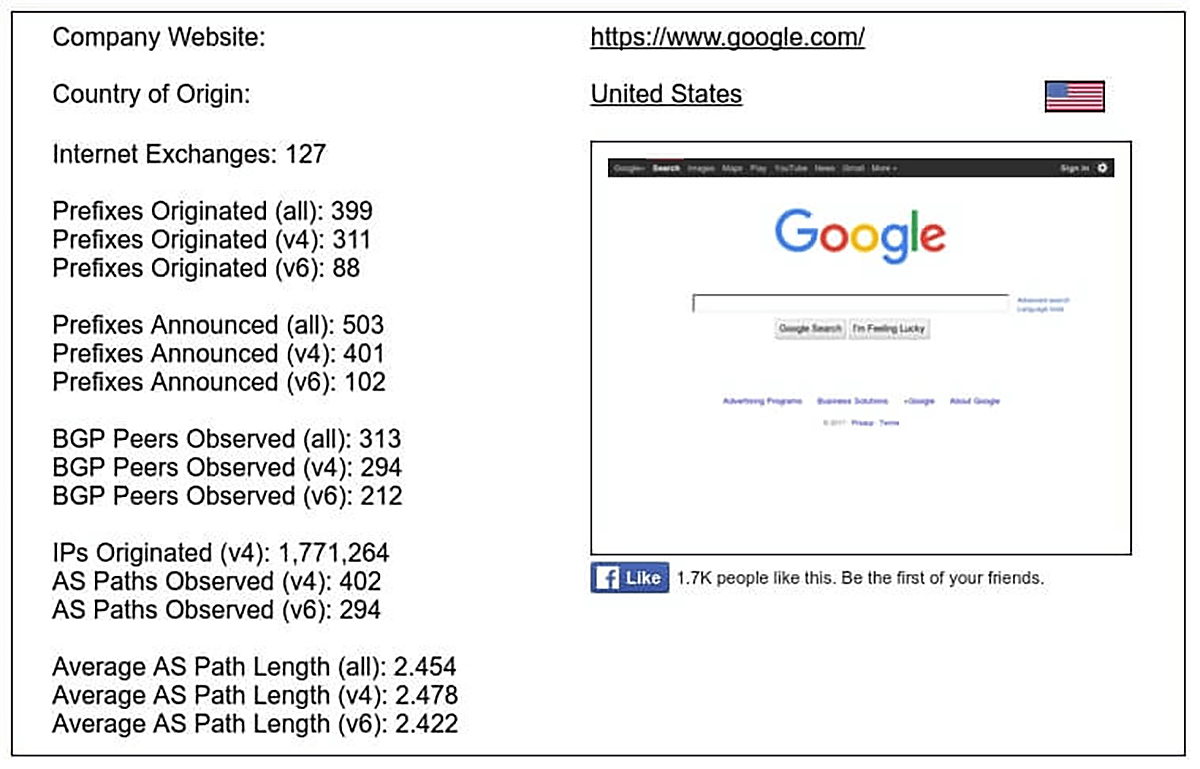
Picture 3 – Google AS 15169 BGP Statistics
The troubleshooting utilities such as ping and traceroute are often included in web based LG interface. They are great tools enabling network administrators to check a network connectivity from remote AS to their networks or to trace the routers along the path. Below is an output of the
trace test to the IP address 8.8.8.8 – Google public DNS service run on Eastlink LG. It gives us a list of the routers on the path between AS7018 (AT&T) and AS15169 (Google).
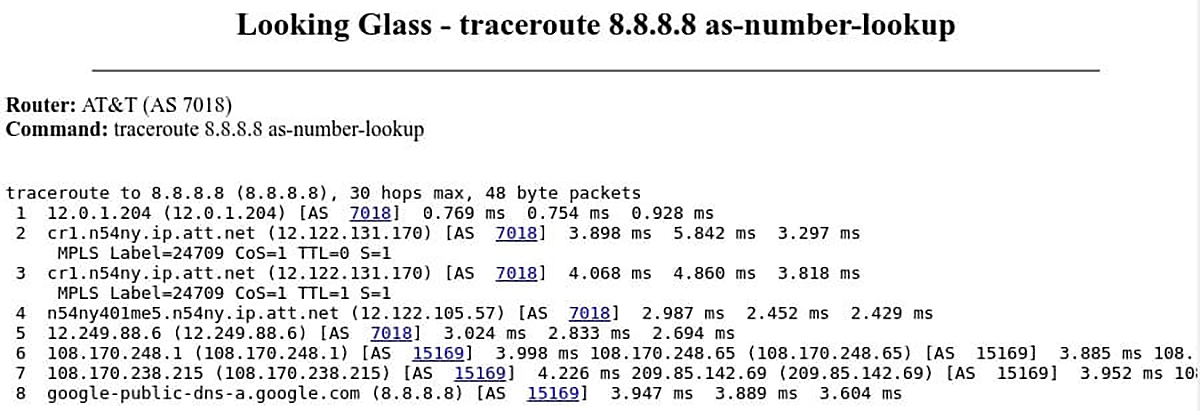
Picture 4 – Traceroute Command Issued on LG Server for AS 7018 (AT&T)
CLI Looking Glass Servers
The web based LGs are certainly a good place to start when we want to find out how our prefixes are propagated in the Internet. However, a web interface usually offers limited access to show BGP command and its subcommands. For this reason, the best LG servers are public route servers that simplify peering between BGP peers and very often offer access using telnet protocol. A telnet session is limited to a read only access. Public route servers are commercial routers from vendors such as Cisco or Juniper or they are Linux boxes running open source routing daemons such as Quagga or Bird. Here is a general list of public route servers. Let’s telnet to a public AT&T route server for AS 6500 (private AS) which is running JUNOS. We will check a route for the prefix 8.8.8.0/24. As it is a public route server, login credentials are posted as a part of the banner, usually at the bottom. Login with username
‘rviews’, password ‘rviews’.
$ telnet route-server.ip.att.net
rviews@route-server.ip.att.net> show route 8.8.8.0/24 active-path terse
inet.0: 627915 destinations, 9417650 routes (627915 active, 0 holddown, 0 hidden)
+ = Active Route, – = Last Active, * = Both
| A V Destination | P Prf | Metric 1 | Metric 2 | Next hop | AS path |
| * N 8.8.8.0/24 | B 170 | 100 | 7018 15169 I | ||
| unknown | >12.0.1.1 |
The command above inspects a routing table for the entry 8.8.8.0/24. The route to a network 8.8.8.0/24 was learnt via BGP protocol. Packets with destination address 8.8.8.8 will be sent to the AS 15169 via AS 7018.
The command below provides detailed information about a route to 8.8.8.0/24. We can see that a local (private) AS is 65000, the BGP peer AS number is 7018 with a router ID 12.122.125.106. Packets to 8.8.8.0/24 will be routed via interface em0.0 to the next hop IP address 12.0.1.1.
rviews@route-server.ip.att.net> show route protocol bgp 8.8.8.0/24 active-path extensive
inet.0: 625872 destinations, 9387008 routes (625872 active, 0 holddown, 0 hidden)
8.8.8.0/24 (15 entries, 1 announced)
*BGP Preference: 170/-101
Next hop type: Indirect
Address: 0x225602c
Next-hop reference count: 697731
Source: 12.122.125.106
Protocol next hop: 12.122.125.106
Indirect next hop: 0x2 no-forward INH Session ID: 0x0
State:
Local AS: 65000 Peer AS: 7018
Age: 6d 23:19:43 Metric2: 0
Validation State: unknown
Task: BGP_7018.12.122.125.106+179
Announcement bits (1): 3-Resolve tree 2
AS path: 7018 15169 I
Communities: 7018:2500 7018:37232
Accepted
Localpref: 100
Router ID: 12.122.125.106
Indirect next hops: 1
Protocol next hop: 12.122.125.106
Indirect next hop: 0x2 no-forward INH Session ID: 0x0
Indirect path forwarding next hops: 1
Next hop type: Router
Next hop: 12.0.1.1 via em0.0
Session Id: 0x0
12.120.0.0/13 Originating RIB: inet.0
Node path count: 1
Forwarding nexthops: 1
Nexthop: 12.0.1.1 via em0.0
The Looking Glass servers provide a view into the IP routing table of an AS where they are located. They are valuable troubleshooting tool for routing issues, widely used by network engineers.
A ping, traceroute or MTR can be run using BGP Looking Glass from Noction Intelligent Routing Platform Frontend via the default route or via a specific provider. The tool is available under Troubleshooting > Looking Glass.




