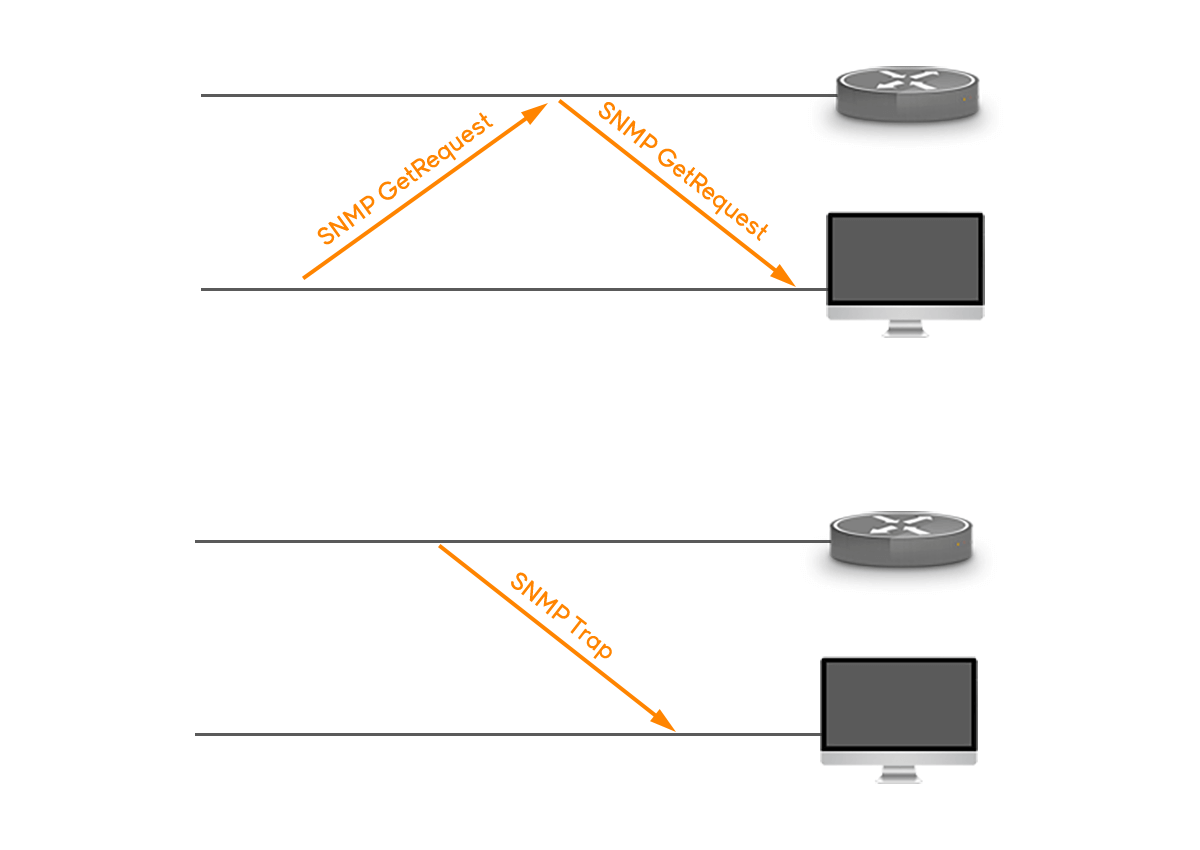
SNMP operates based on a manager-agent model. From an SNMP perspective, “agents” are remote network devices. The agents may vary across different types of networks – from small office to a global telecom network. They can be servers, routers, switches, desktops, or any other compatible devices. A so-called “manager” sends requests and receives agents’ responses in return.
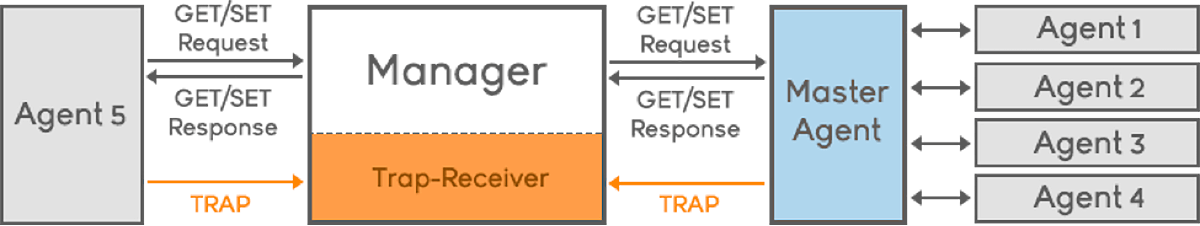
There are five primary types of SNMP messages – TRAP, GET, GET-NEXT, GET-RESPONSE, and SET used as means of communication between the SNMP agent and the SNMP manager.
What are SNMP Traps?
The most frequently used SNMP messages are traps. These are sent to the manager by an agent when an issue needs to be reported. SNMP traps are quite unique if compared to other message types, since they are the only method that can be directly initiated by an SNMP agent. The other types of messages are either initiated by the SNMP manager or sent as a result of the manager’s request. This ability makes SNMP traps indispensable in most networks. It is the most convenient way for an SNMP agent to inform the manager that something wrong is going on.
There are two main methods to send useful data via SNMP traps. The first one is by using the so-called “granular traps”. Granular traps have a unique identification number (OID – “object identifier”) that allows the SNMP manager to distinguish them from each other. The meaning of each OID is stored in a translation file called Management Information Base (MIB) which is addressed by the SNMP manager in order for it to understand the trap sent by the agent.
Thanks to the above method, the actual trap sent by the agent does not have to carry any information about the alert, since all of the details are available in the MIB. Only the OID is needed for the manager to look up the information in the MIB. This minimizes the bandwidth used by the trap.
The second way of transmitting useful information using SNMP traps is to incorporate the alert data within the traps themselves. In this case usually all the traps have the same OID. In order for the manager to understand these kind of traps, it needs to process the information contained in the trap. Data is encoded within an SNMP trap in a typical key-value pair configuration. These pairs are called “variable bindings” and they contain extra information relating to the trap. For instance, an SNMP trap might contain variable bindings for “domain name”, “urgency level”, and “alert description”.
To conclude, SNMP trap is a widely used mechanism to alert and monitor a devices’ activities across a network. With that being said, Noction has also added this capability to it’s Intelligent Routing Platform. IRP produces a vast number of various events and majority of them are critical for administrators’ awareness. Operations can decide upon which events should trigger notifications and then configure them on IRP. Such events include:
- Excessive loss detected towards a destination prefix
- Excessive latency detected towards a destination prefix
- Outage detected towards a destination prefix
- A BGP session with one of the providers goes down
- The PBR policies configured on the edge router are not properly working
- Plus many more, which can easily be configured.
Currently the platform supports only traps for version SNMPv2. These are generated by the IRP components and are disabled by default. Besides notifying about events occurring in the network, the traps also include the list of Variable Bindings (varbinds) with detailed information related to a particular trap.
To see the exact IRP parameters that need to be switched on for a specific trap to work, please check section 4.1.9 Traps parameters in IRP Installation and Configuration Guide.
Read this article in French – Les Traps SNMP expliqués: messages SNMP et paramètres des traps
Read this article in Spanish – El Protocolo SNMP Explicado: Trampas SNMP
Read this article in Portuguais – Protocolo SNMP e Suas Traps: Explicação e Tendências




