 The Internet is for everyone, yet not everyone accepts that. In light of the news about Cogent Communications and Lumen Technologies disconnecting clients in Russia, we will discuss restrictions that the Russian Federation has imposed on social media and the potential tech scenarios where the whole country gets isolated or ends up with limited access to the Internet.
The Internet is for everyone, yet not everyone accepts that. In light of the news about Cogent Communications and Lumen Technologies disconnecting clients in Russia, we will discuss restrictions that the Russian Federation has imposed on social media and the potential tech scenarios where the whole country gets isolated or ends up with limited access to the Internet.1. Blocking Access to Social Media in Russia
Although not technically a disconnection from the internet, the blocking of some global social media websites in March 2022 may have given users in Russia the impression that they’ve been partially disconnected from the Internet.
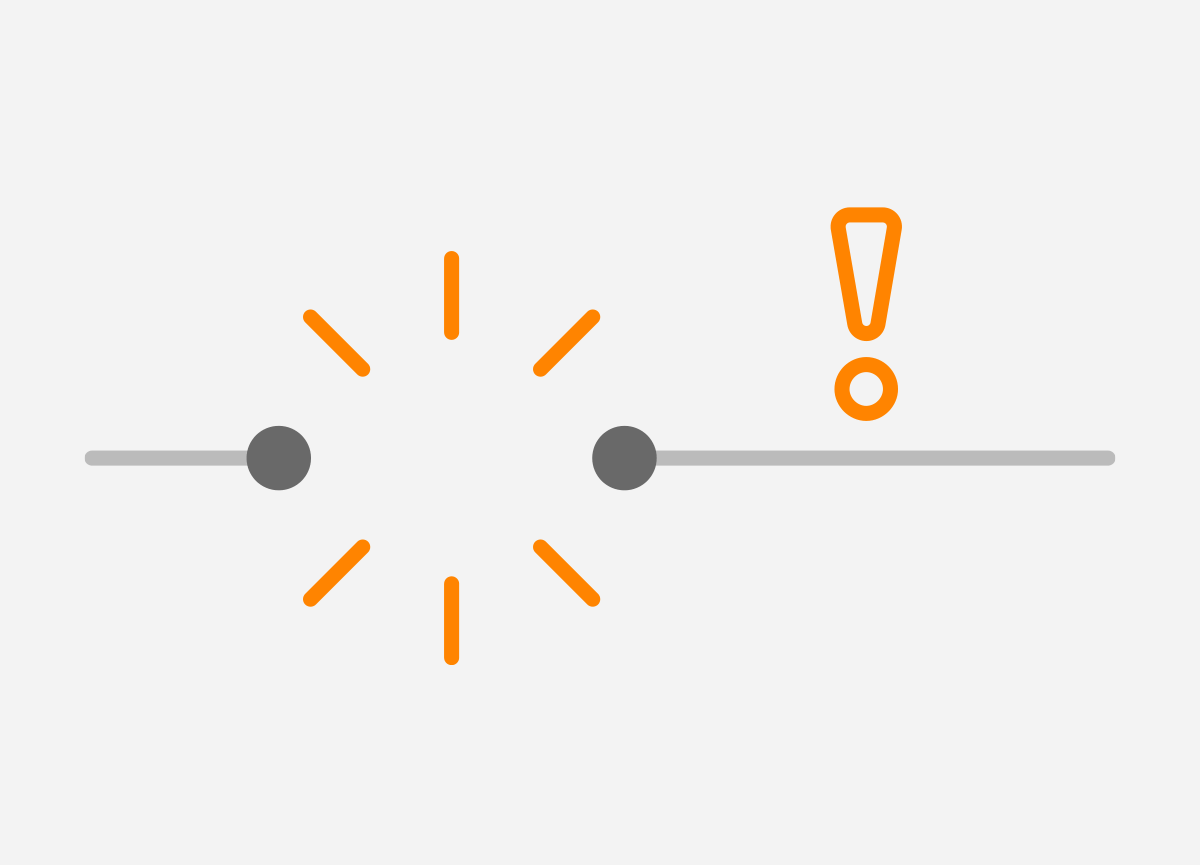
On March 4th, 2022, Roskomnadzor (Federal Service for Supervision of Communications, Information Technologies and Mass Media) blocked access to Facebook and Twitter. A check of Facebook’s availability using the https://globalcheck.net site on March 28 shows that traffic, although severely limited, has not been completely blocked (Figure 1).
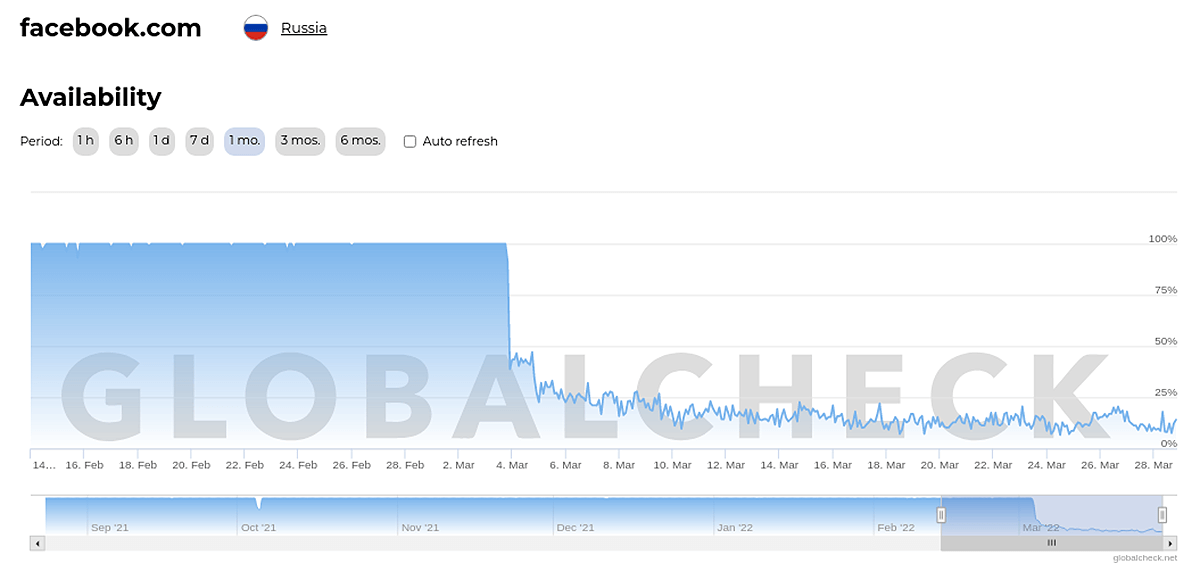
Figure 1 – Facebook Availability from Russian Federation
As for access to Twitter from Russia, traffic dropped to 50% since the 26th of February and continued to fall below 25% as of March 4th (Figure 2).
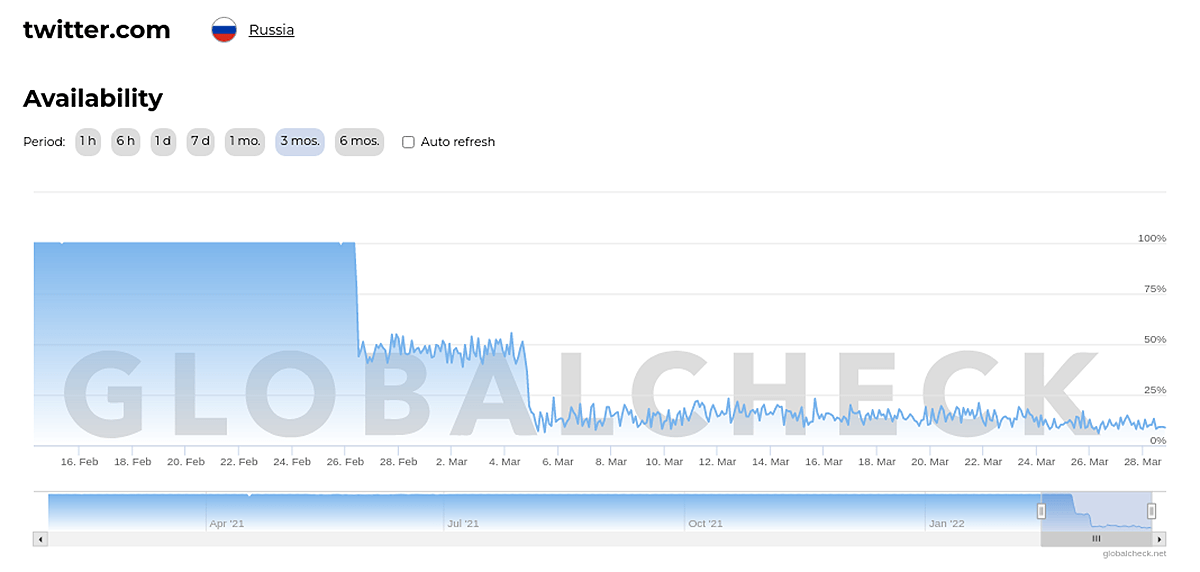
Figure 2 – Twitter Availability from Russian Federation
Access to Instagram from Russia was blocked on March 14th (Figure 3), with users given an additional 48-hour period to transfer their photos and videos to other social networks and to notify their contacts and subscribers.
Figure 3 – >Instagram Availability from Russian Federation
The growing demand for VPN services in Russia reveals that users use VPNs to bypass restrictions on access to social platforms and blocked websites.
VPN apps are among Russia’s most popular free apps on the App Store and Google Play. For example, on the 28th of March, VPN apps were in the top two spots in the iPhone App Store, with four VPN apps in the top ten (Figure 4).
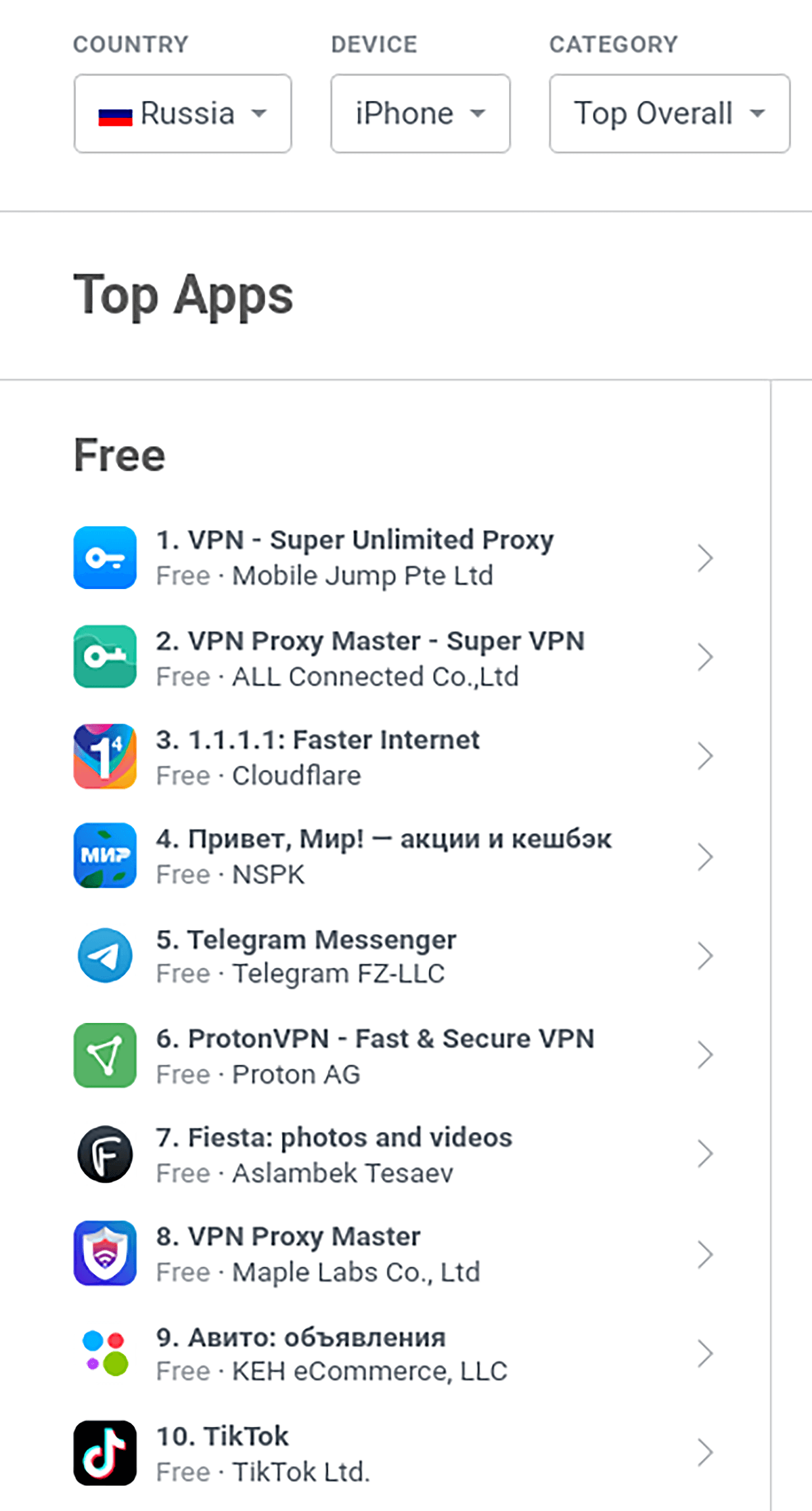
Figure 4 – Top 10 Ranked iPhone Apps in iOS App Store on March 28th
https://appfigures.com/top-apps/ios-app-store/russia/iphone/top-overall
Similarly, of the top ten Google Play apps, there are three VPN apps (Figure 5).
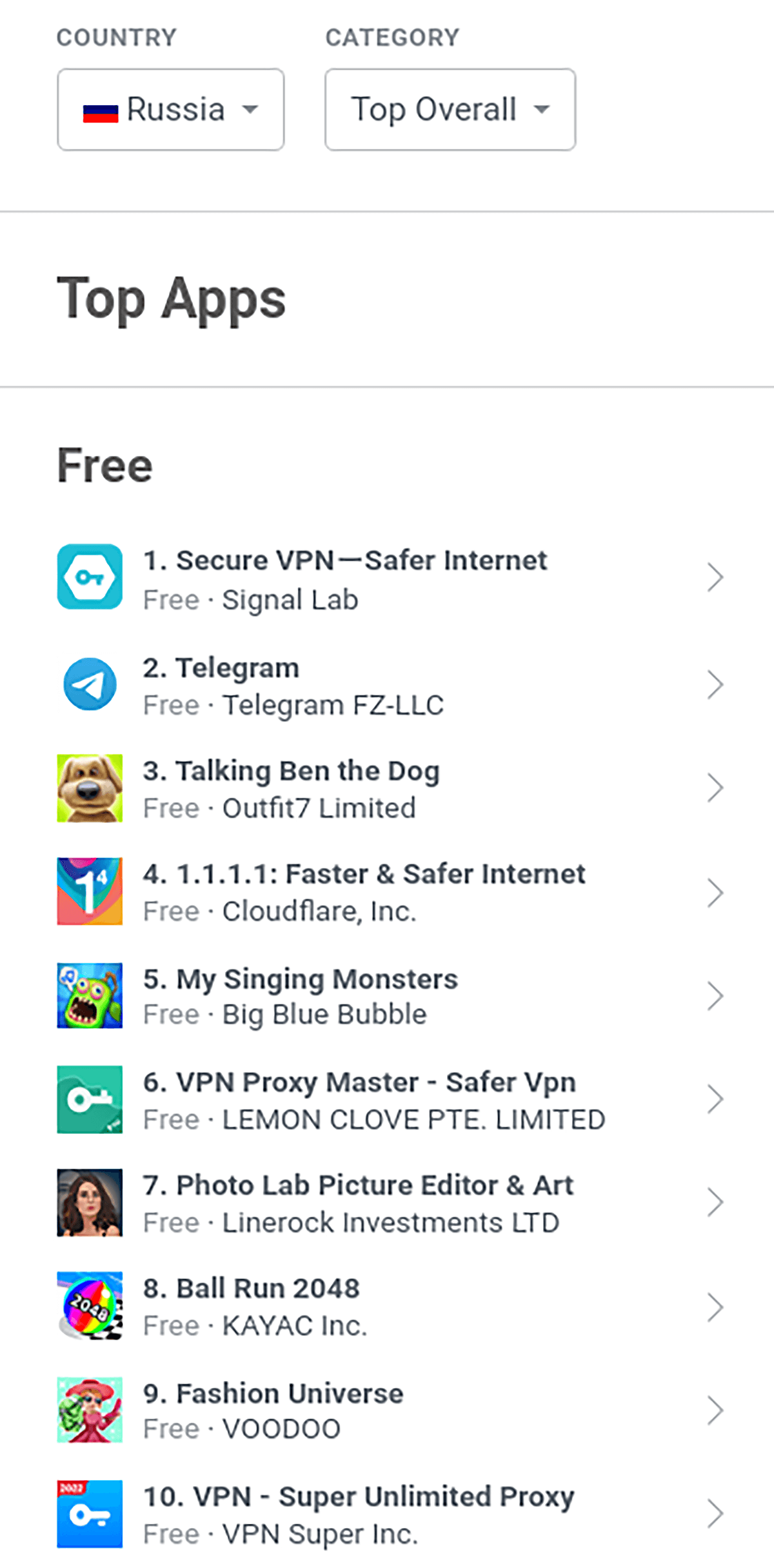
Figure 5 – Top 10 Ranked Google Play Apps on March 28th
https://appfigures.com/top-apps/google-play/russia/top-overall
While many try to get around restrictions using a VPN service, some social media can also be accessed on Darknet. Twitter, for example, entered the Darknet after being blocked by the Russian government, with its union website accessible via the Tor browser.
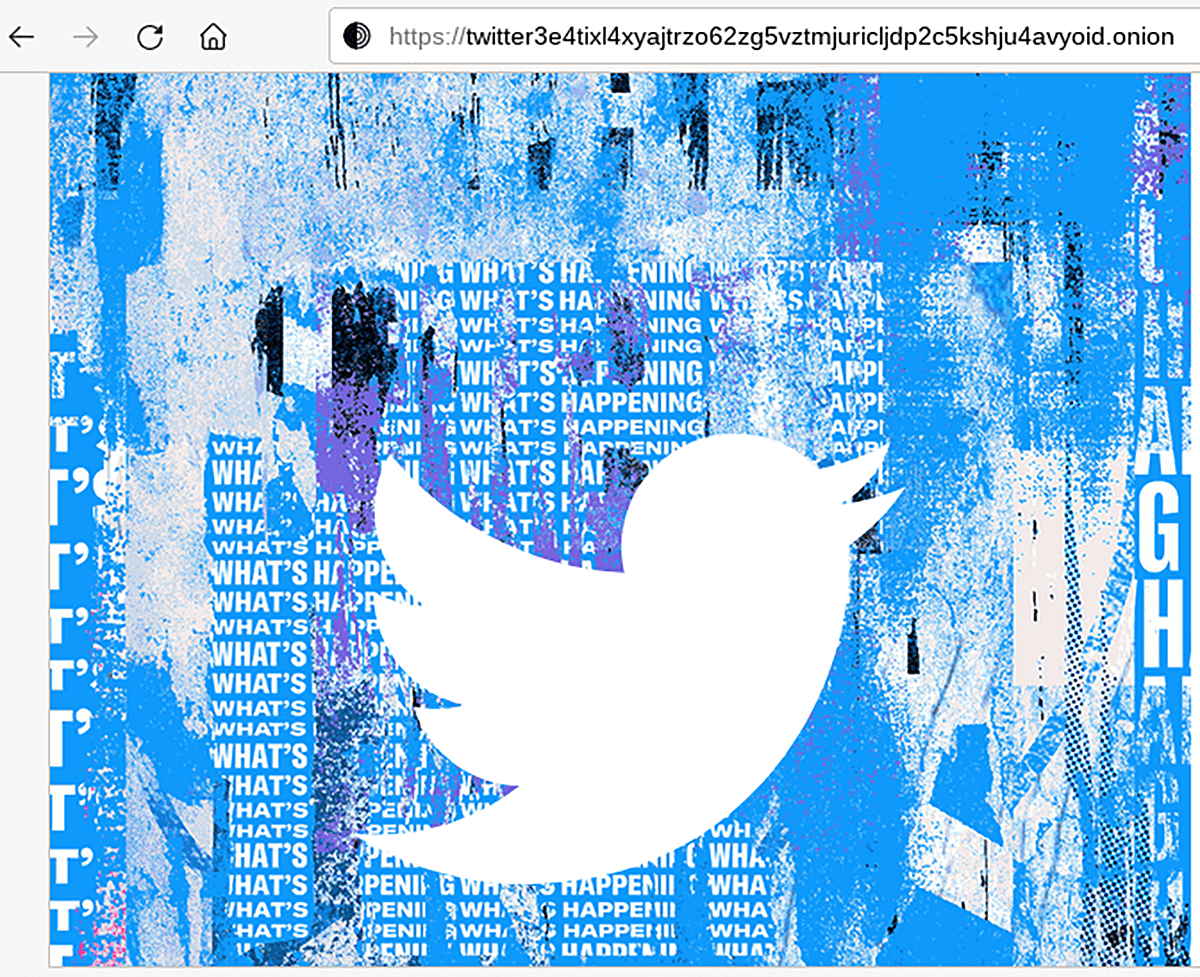
Figure 6 – Twitter Union Website
2. Isolating Russian Federation from the Internet by Western Companies
So far, we have talked about the blocking of websites by the Russian Federation authorities. Another challenge that Russian users face is the shutting down of Internet services by Western companies.
Cogent Communications (AS174) disconnected Russian customers from the Internet on March 4th. Cogent is one of the world’s largest Internet backbone operators and, until now, has sold transit to Russia’s PJSC Rostelecom (AS12389, AS34584).
This does not mean that Russia has been cut off from Internet access, as Russians also buy transit from other ISPs. Therefore, Rostelecom’s prefixes continue to be advertised via BGP to other Autonomous Systems (AS) (Figure 7).
However, Rostelecom’s disconnection indeed leads to slower international connectivity and possible congestion as the total available bandwidth for the Russian Federation’s international connectivity has been reduced.
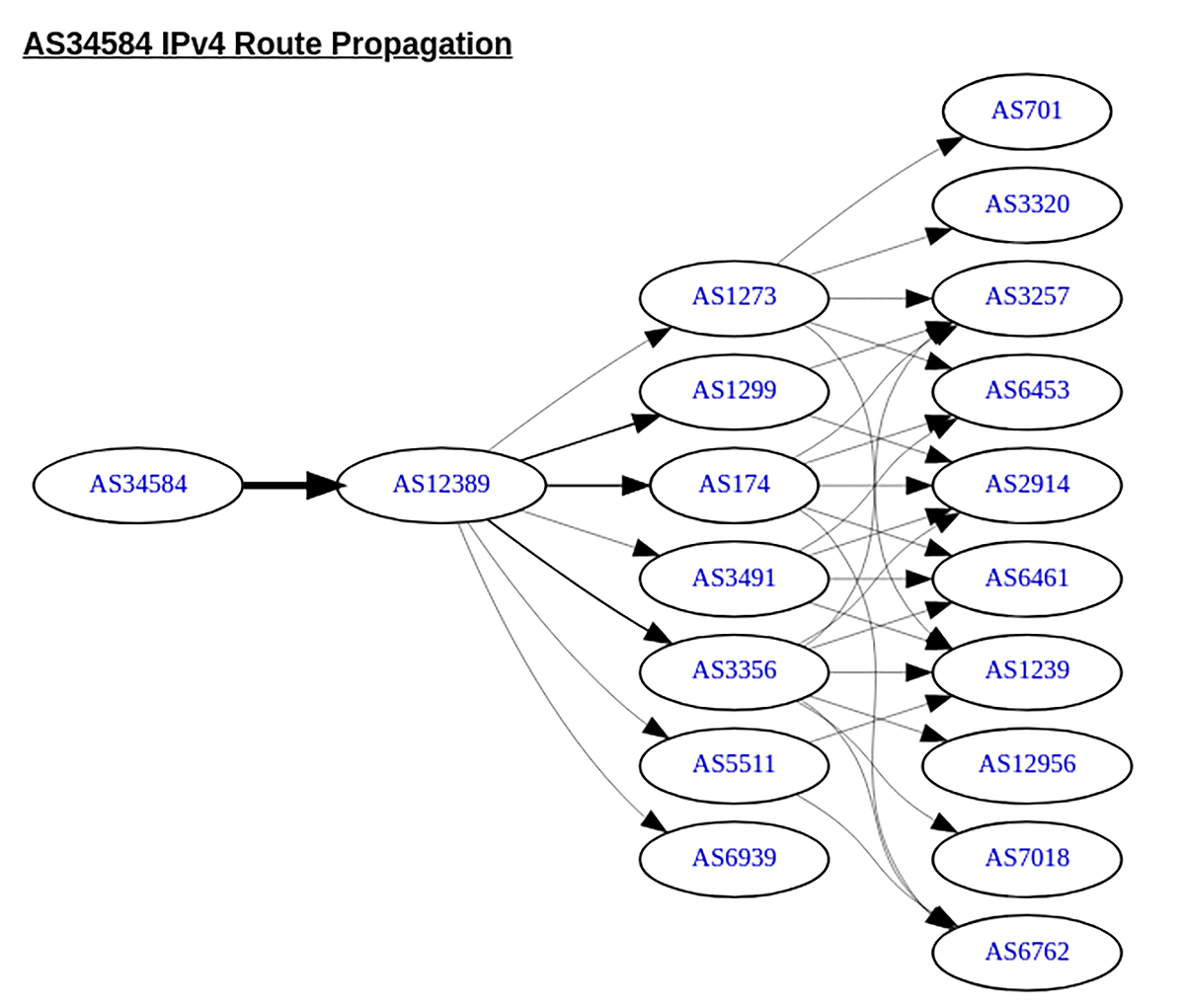
Figure 7 – Propagation of Rostelecom IPv4 Prefixes
https://bgp.he.net/AS174#_graph4
We use the Cogent Looking Glass service to check if Rostelecom prefixes are advertised to Cogent Communications. The 92.37.128.0/17 prefix, originated on AS34584 (Rostelecom), is advertised to AS12389 (Rostelecom). AS12389 advertises this prefix to AS 174 (Cogent Communications) (Figure 8).
AS12389 is prepended three times to make the path to AS 34584 less preferable for the BGP best path selection algorithm, but it is still the best path and is therefore installed in the routing table of the Cogent network device.
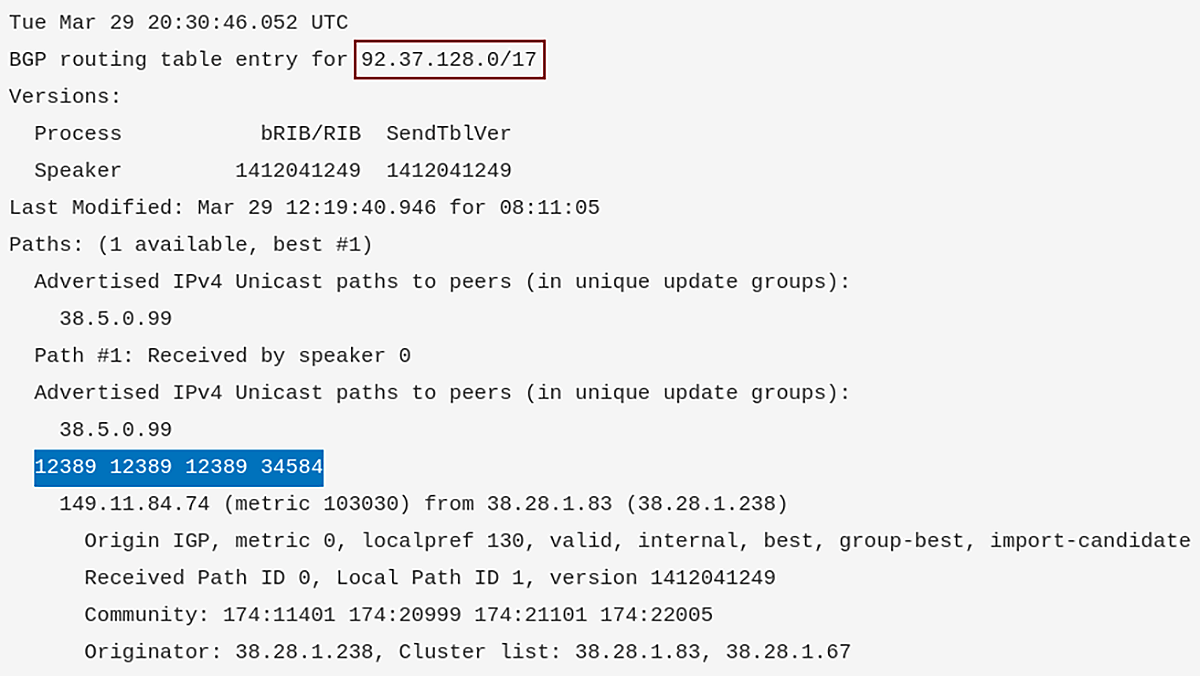
Figure 8 – BGP Route Lookup for Prefix 92.37.128.0/17 (Rostelecom) Using Cogent Looking Glass
https://www.cogentco.com/en/looking-glass
Another U.S. Internet backbone provider, Lumen Technologies Inc (formerly CenturyLink), announced on the 8th of March that it was ceasing operations in Russia. The operator said it continues to provide services to ISPs outside Russia that are directing traffic into the country (Figure 9).
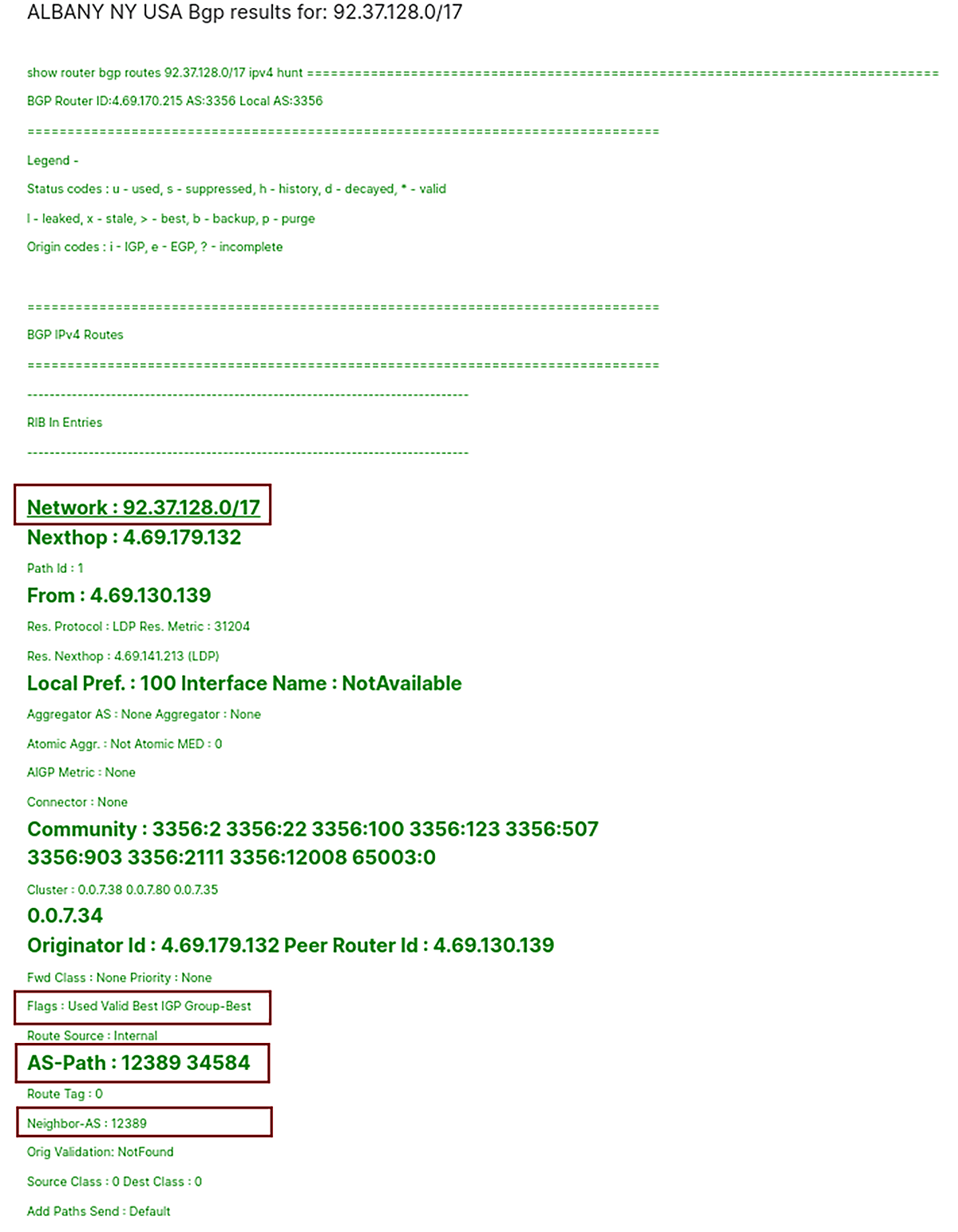
Figure 9 – BGP Route Lookup for Prefix 92.37.128.0/17 (Rostelecom) Using Lumen Looking Glass
https://lookingglass.centurylink.com/
2.1. Revocation of IP Address Ranges
RIPE NCC is the regional registry (RIR) responsible for the allocation and administration of IP addresses to ISPs for Europe, the Middle East, and parts of Central Asia. With more than 45.5 million IPv4 addresses, Russia holds the sixth-largest number of any country in the RIPE NCC service region [1].
According to John Levine, “If RIPE were to revoke all of the IP addresses assigned to Russian networks, and those Russian networks continued announcing routes to their formerly allocated addresses, there is not much anyone could do about it. Hypothetically RIPE could reassign the addresses to other people, but that would cause chaos with dueling route announcements, so, fortunately, they won’t be doing that.”
Of course, ISPs do not have to accept Russian traffic, and they can configure their network to reject packets from Russian IP addresses. However, they do not need help from ICANN or RIPE to do so.
2.2 DNS
The Domain Name System (DNS) is a fundamental service for the functioning of the Internet, which translates domain names into IP addresses. The mapping of domain names to IP addresses works in a hierarchical order using DNS zones.
Root servers serve the root zone, which tops the hierarchy, and publish the root zone file. The root zone is the global list of top-level domains that contains the generic top-level domains (.com, .net, .org), country code top-level domains ( .ru, .su), and internationalized top-level domains which are ccTLDs written in the countries local characters (e.g. .рф).
There are 13 logical root name servers specified, with logical names in the form letter.root-servers.net, where the letter ranges from a to m [2]. All root servers are independent.
RIPE NCC operates k.root-servers.net, one of the 13 Internet root name servers. The K-root service is provided by a set of distributed nodes using IPv4 and IPv6 anycast. Each node announces prefixes from 193.0.14.0/23 in AS25152.
There are K-root servers in Russia in the following cities under RIPE control (Figure 10):
Novosibirsk
Saint Petersburg
If RIPE NCC were to revoke the “.ru”, “.рф”, and “.su” domains and shut down all root name servers in Russian, the Internet would cease to function in Russia. This scenario is improbable, as IANA has already denied Ukraine’s February 28th request to shut down DNS service in Russia.
In addition, likely, the Russian Federation has already built its own root and anycast servers. This hypothesis may be supported by an alleged document on Russian Internet politics published by NEXTA, a free Belarusian news service based in Warsaw. It stated that all Russian websites were to switch to the Russian Domain Name System (DNS) service by Friday, March 11th.
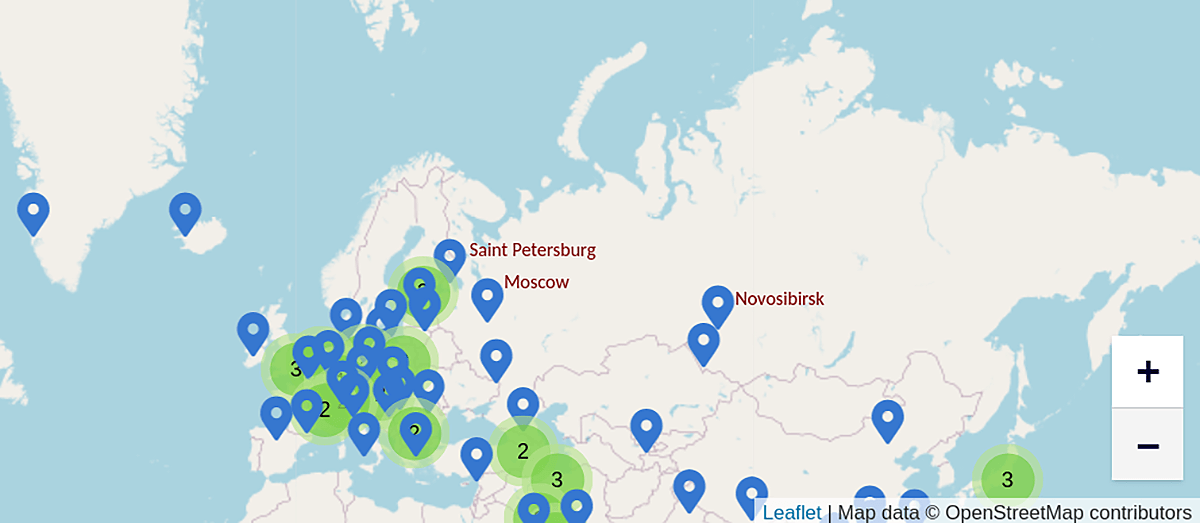
Figure 10 – K-Root Servers in Russian Federation
https://www.ripe.net/analyse/dns/k-root
2.3 Revocation of TLS Certificates
TLS certificates help the web browser confirm that a domain belongs to a verified entity and that the exchange of information between the user and the server is encrypted.
Russia has created its own domestic TLS certificate authority (CA) to bypass sanctions imposed by western companies and governments that would prevent Russian sites from renewing existing TLS certificates, causing browsers to block access to sites with expired certificates. Sites are encouraged to replace the foreign security certificates if such are revoked or expire (Figure 11).
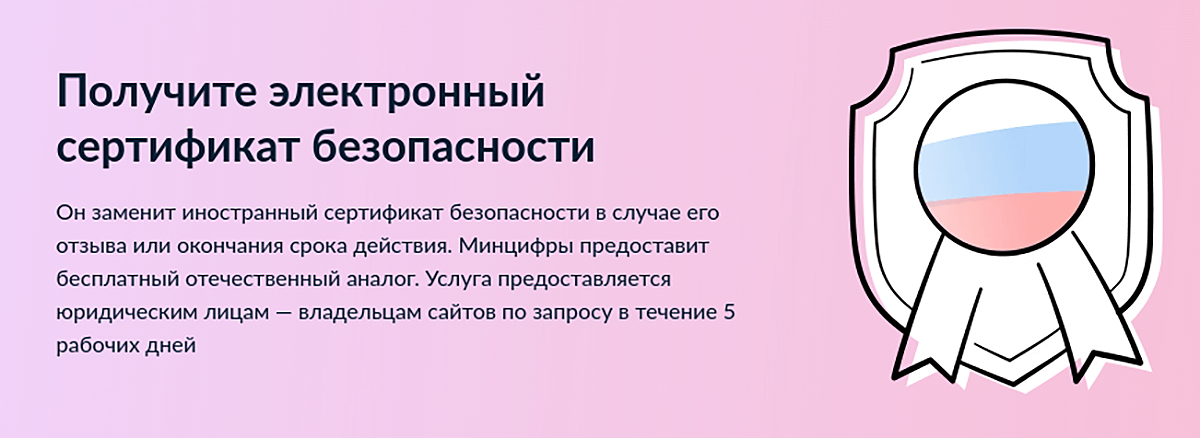
Figure 11 – Russian Web Site for Requesting Free TLS Certificate
https://www.gosuslugi.ru/tls
The Russian root TLS certificate is currently not included in the storage of root certificates of operating systems and main browsers (Figure 12). The only web browsers that recognize Russia’s new CA as trustworthy are the Russia-based Yandex browser and Atom products, so Russian users are told to use these instead of Chrome, Firefox, Edge, etc.
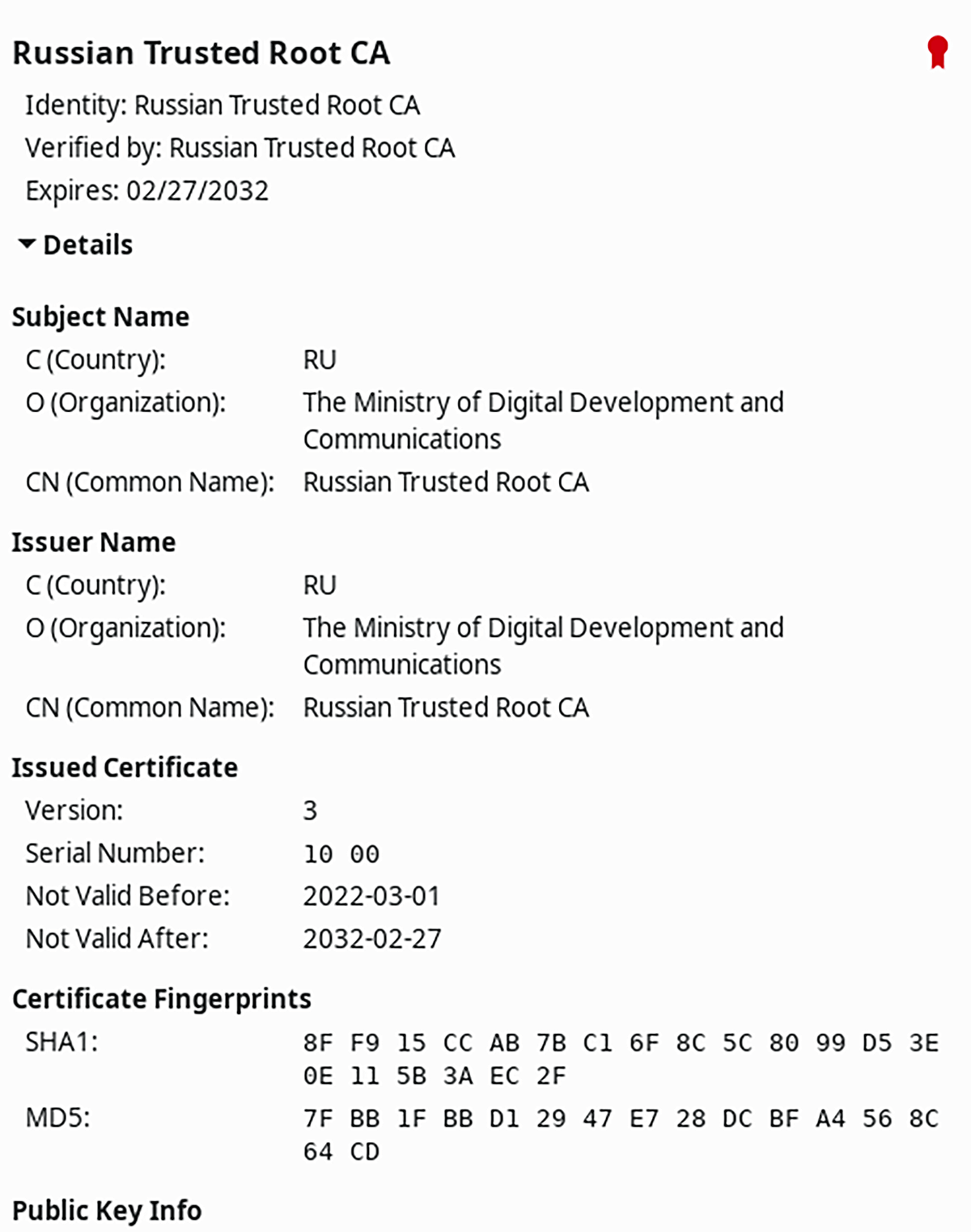
Figure 12 – Russian Trusted Root CA Certificate Valid for 10 Years
Conclusion
Apart from the shutdown of Cogent and Lumen services in Russia, there haven’t been any other attempts to isolate the Russian Federation population from the Internet from abroad. Our blog post described the current and hypothetical Internet blockage scenarios (both internal and external) for Russia and the attempts of the Russian government to control Internet access as well as to mitigate the imposed/potential Internet access restrictions.




